-
How to CISO, Volume 1: The First 91 Days

Just want to download the eBook? Head over to How to CISO, Volume 1: The First 91 Days! It seems to be a rite of passage for all CISOs to, at some point in their career, write down their advice for other CISOs starting a new job, whether they are a first-time or veteran CISO.
Security Talks
-
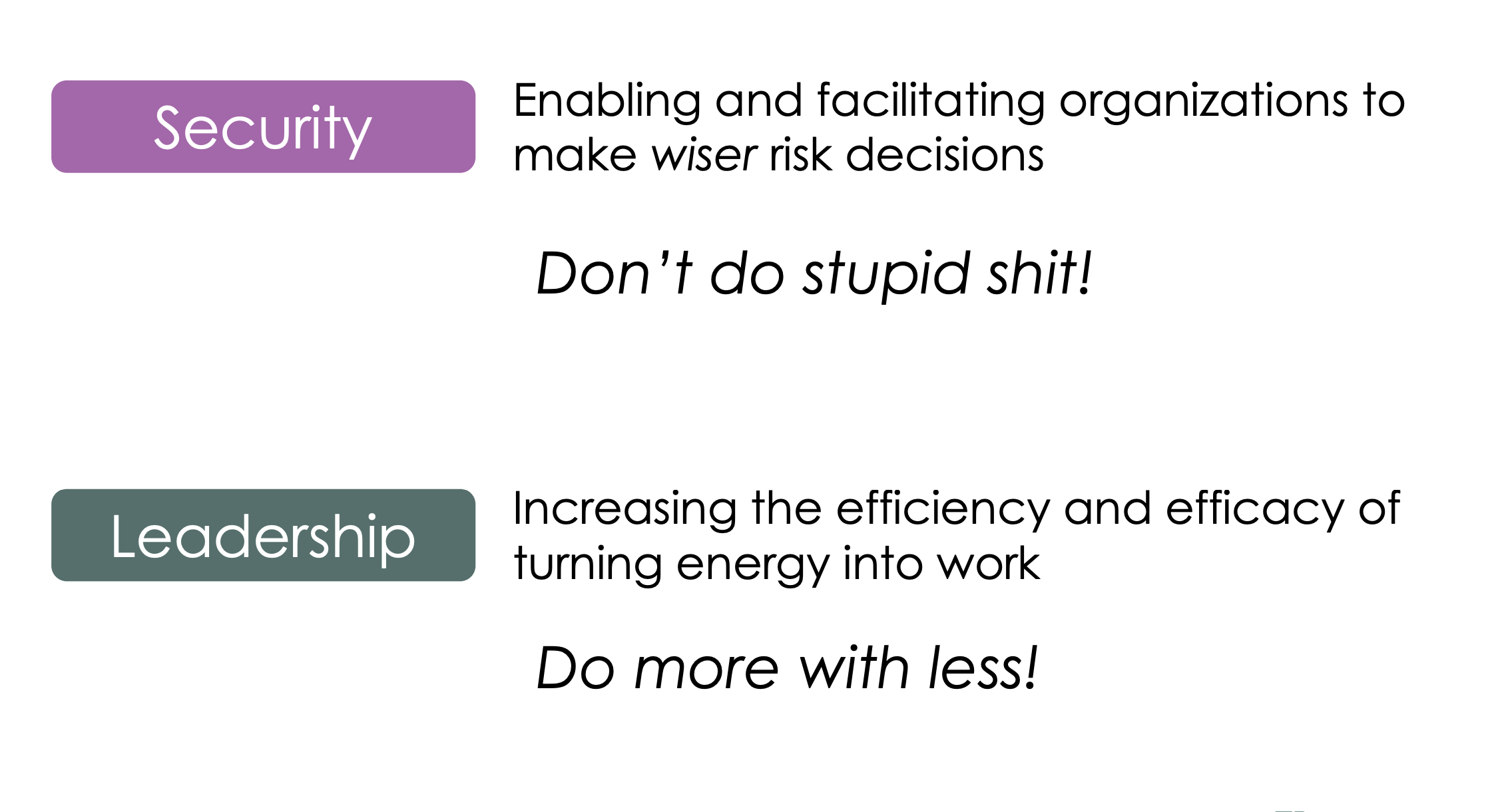
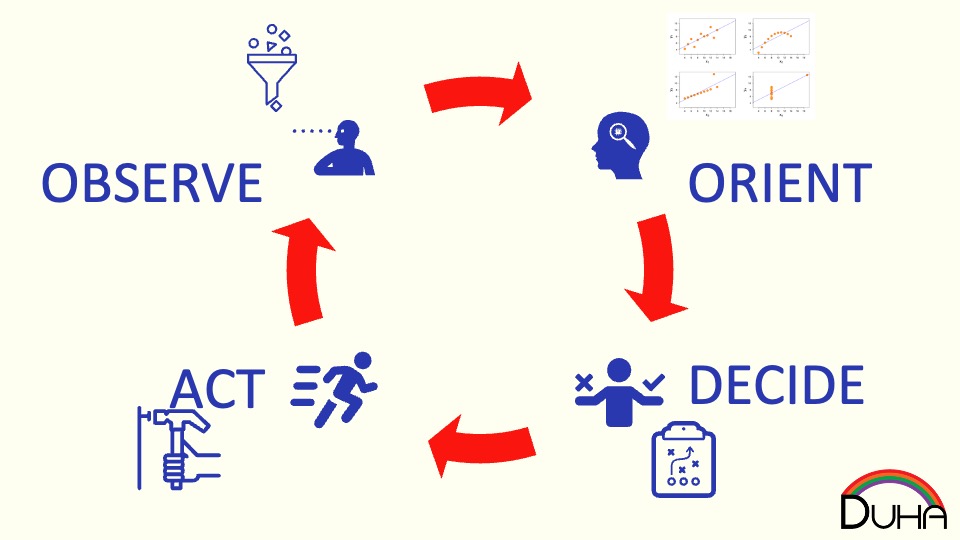
This talk delves into the intersection between security–helping make wiser risk choices–and leadership–getting more done with a lower energy cost. It draws on the lessons of the Six Leadership Disciplines and Humans are Awesome at Risk Management talks, providing a handful of examples of specific leadership skills to practice. The 24 skills in the matrix…
-
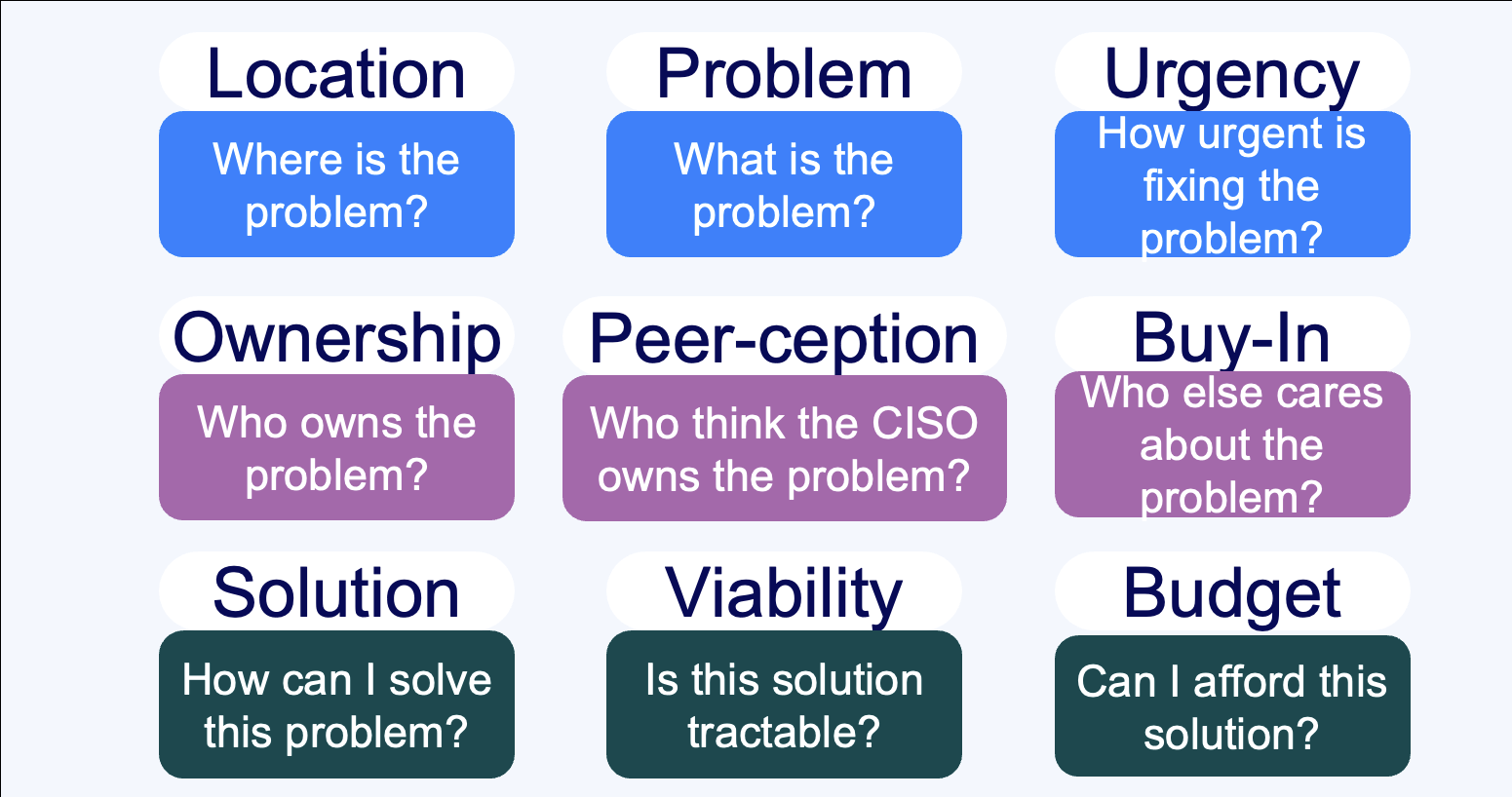
Summary Everybody sells, right? Wrong. Unless you’re taking an order and retiring your quota, you don’t sell – instead, you market. If you’re selling to a CISO, you need to understand the organizational dynamics that surround a CISO’s decision-making process. This talk walks through nine critical questions that CISOs need to understand the answers to…
-
How do you know what to invest in next, or whether the time and energy that you’re spending on a security technology or program is a good investment? Learn how veteran CSOs think about security investments, and develop your own rubric for evaluating where to best make your next security improvement.
-
How do you design defenses against DDoS? And how do you think about them from a policy perspective?
-
How do humans make risk decisions, and are they good, bad, or something else?
-
How do the grand challenges of the future look like the grand challenges of the past?
-
What does a Zero Trust journey look like? Explore how we migrated Akamai to a zero trust network access model, before that was even a phrase people knew.
Security Panels
-
Lenovo Late Night I.T: Cybersecurity: Trust No One
Join Baratunde Thurston, Tim Brown, and Andy Ellis as they demistify security.
-
Cyberweek 2021: Navigating the CISO-Vendor relationship
The panel discusses the do’s and don’ts of engagements between CSOs and early-stage startups, the concerns around long integration cycles, the value in quick implementations, and the need to show value quickly.
-
Cyberweek 2021: YL Ventures & Scale Fireside Chat
YL Ventures and Scale Venture Partners hosted a Cyber Week 2021 Fireside chat where Wendy Nather, Sounil Yu, Ryan Gurney, and Ariel Tseitlin discussed the cyber industry challenges and trends. They talked about the burning challenges and the basics that CSOs are still struggling with, and how ransomware attacks undermine our ability to recover. Other…
Security Blog
-
CISOs are still chiefs in name only
If you’re not in the meeting where decisions are made, then you’re not part of the C-Suite—whatever your title may be. Look around the CISO community, and you’ll find signs of burnout everywhere. Where CISOs aren’t just quitting, you’ll find increasing tension between them and their executives, sometimes resulting in surprising departures. Ply a friendly CISO with…
-
Drop the SBOM
Software bills of material are having a moment, but the costs of an externally visible SBOM are likely to outweigh the benefits, says Andy Ellis. There’s a big movement afoot to move to an SBOM-oriented world. If you’re new to this acronym, an SBOM is a “Software Bill of Materials.” The idea is that any…
-
Vulnerabilities don’t count
No one outside the IT department cares about your vulnerability metrics (or they shouldn’t, anyway). They care about efficacy. And traditional stats don’t show that. I had a lovely chat with one of my favorite CISOs the other day, helping them think through the security metrics that they report upwards. Front and center, as I…
-
Three Hidden Security Costs Behind Many Failed Projects
As a long-time CISO, I’ve been on the receiving end of … a lot of vendor sales pitches. So much so that I created a quick template to respond to all of those unsolicited messages. For the most part, vendors would either quietly disappear, or reply with good grace (for many sales development representatives, even being acknowledged…
-
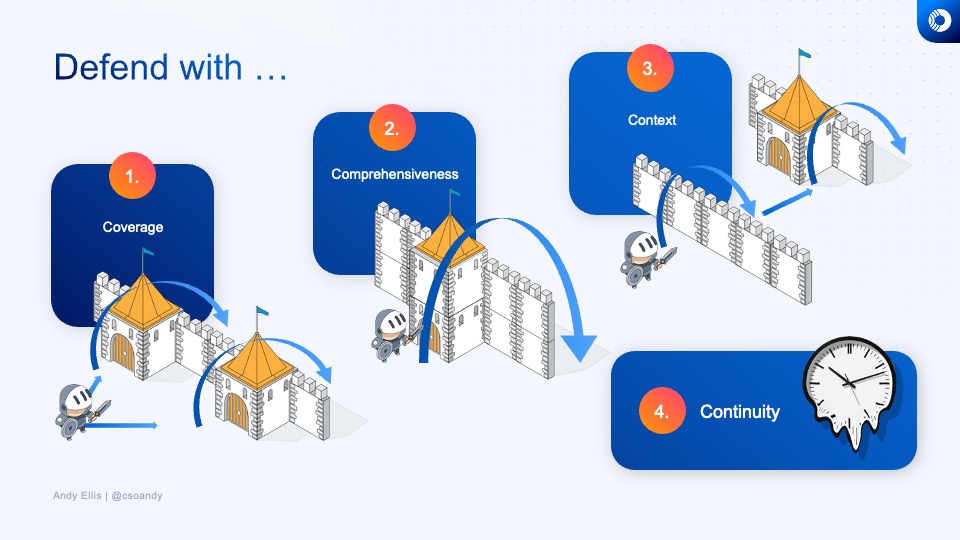
The Fourth Dimension of Risk Management
When security professionals talk about risk, especially with business executives, we often use metaphors rooted in the physical world. We might talk about coverage, and compare it to the length of a wall that surrounds a group of assets. Perhaps we talk about the height of the wall, to consider how comprehensive our defenses are.…
-
Four considerations for improving cloud security hygiene
We think we understand what hygiene is, but what about cloud security hygiene? It’s not like our computers have teeth to brush. Although, if you have a child, you might be familiar with the challenges involved in even basic hygiene. Some of us might even have had conversations like this: “Did you brush your teeth?”“Yes!”You smell in…
-
Risk at the Margin
Humans are, generally, pretty awesome at risk management. Why, then, do we seem to be so bad at it – and in so many different ways – when it comes to assessing risk in the CoViD era? Risk Models First, let’s talk about how humans make most risk decisions. Risk comes in a lot of different flavors…
-
Understanding Risk
Operating or overseeing a business – whether it’s as a director, executive, or manager – requires an understanding of risk, and especially how it impacts your strategy. But risk is a nebulous concept. It means something different to everyone, so it helps to levelset not just on a working definition of risk, but on approaches…
-
Football. CoViD-19, and distributed systems hazards
Looking at the latest trickle of Covid-19 cases in the NFL – specifically in the Patriots locker room – it strikes me that some of the challenges of public health safety are strikingly similar to the issues of distributed system safety in computer systems, and each can help highlight important lessons in the other. Caveats: …
-
One company’s successful approach to gender balance
In an industry where 10-15% of staff are women, the InfoSec team at Akamai—a cybersecurity, content-delivery network and cloud-service provider—is now 40% women. Driving that change—from 28% two years ago—took only a few, simple practices that might work in many other organizations. We drove those changes in partnership between the talent-acquisition team and the hiring managers;…
Security Podcasts
-
Why Aren’t You On Slack Where I Can Interrupt You?
https://cisoseries.com/why-arent-you-on-slack-where-i-can-interrupt-you/ This week’s episode is hosted by David Spark (@dspark), producer of CISO Series and Andy Ellis (@csoandy), operating partner, YL Ventures. Our guest is Howard Holton, CTO, GigaOm. Full transcript [Voiceover] Best advice I ever got in security. Go! [Howard Holton] Keep it simple. You’re likely overcomplicating it. The reality is we spend a lot of time as technologists kind of buried in technology…
-
This Unwanted Cold Call Made Possible Thanks to This Month’s Sales Quota
https://cisoseries.com/this-unwanted-cold-call-made-possible-thanks-to-this-months-sales-quota/ A CISO calls on security vendors to stop the spamming and cold calling. Are these annoyances the direct result the way salespeople are measured? Is that what drives the desperation and bad behavior? This week’s episode is hosted by David Spark (@dspark), producer of CISO Series and Andy Ellis (@csoandy), operating partner, YL Ventures. Our guest is Dmitriy Sokolovskiy, CISO, Avid. Full…
-
Adversaries Beef Up Their Shiny Object Distraction Campaign
https://cisoseries.com/adversaries-beef-up-their-shiny-object-distraction-campaign/ We are all very easily distracted, and adversaries know that. So they’ll try any little trick to make us not pay attention, look away, or do what we’re not supposed to do all in an effort to break our human defenses. This week’s episode is hosted by David Spark (@dspark), producer of CISO Series and Andy Ellis (@csoandy),…