-
How to CISO, Volume 1: The First 91 Days

Just want to download the eBook? Head over to How to CISO, Volume 1: The First 91 Days! It seems to be a rite of passage for all CISOs to, at some point in their career, write down their advice for other CISOs starting a new job, whether they are a first-time or veteran CISO.…
Security Talks
-
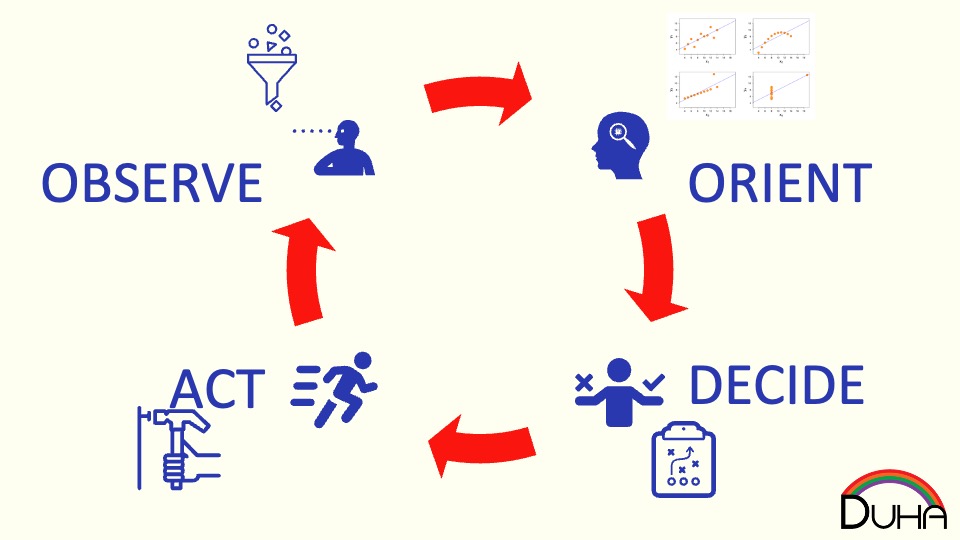
This talk delves into the intersection between security–helping make wiser risk choices–and leadership–getting more done with a lower energy cost. It draws on the lessons of the Six Leadership Disciplines and Humans are Awesome at Risk Management talks, providing a handful of examples of specific leadership skills to practice. The 24 skills in the matrix…
-
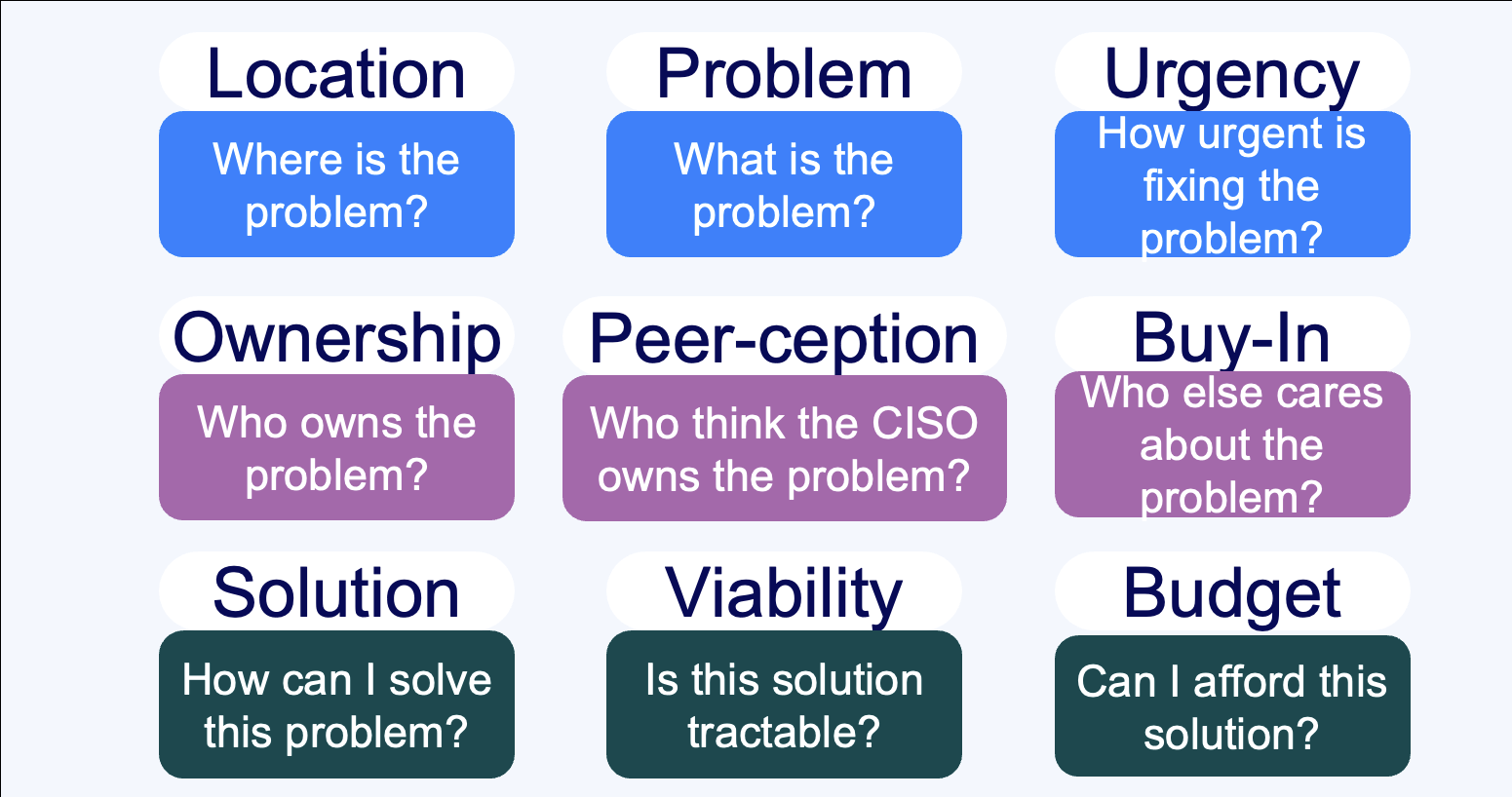
Summary Everybody sells, right? Wrong. Unless you’re taking an order and retiring your quota, you don’t sell – instead, you market. If you’re selling to a CISO, you need to understand the organizational dynamics that surround a CISO’s decision-making process. This talk walks through nine critical questions that CISOs need to understand the answers to…
-
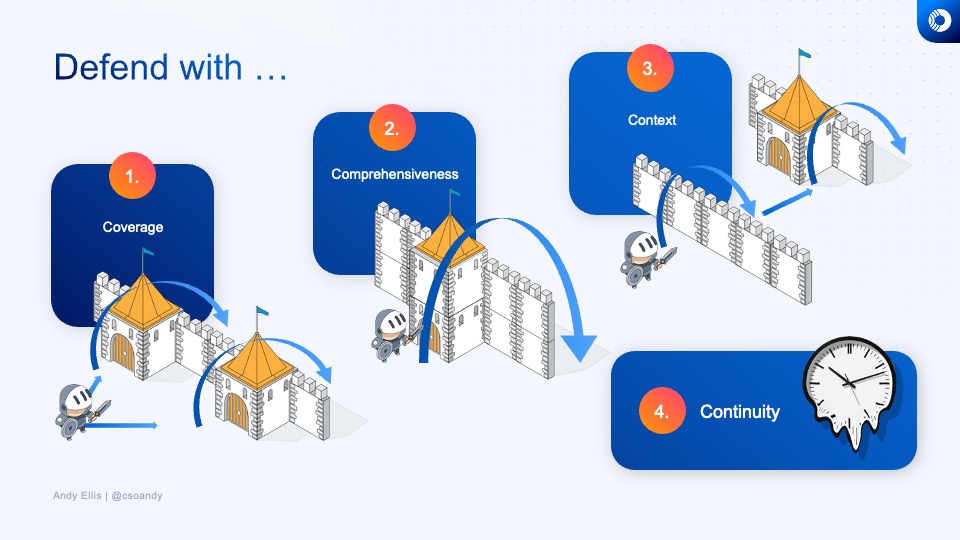
How do you know what to invest in next, or whether the time and energy that you’re spending on a security technology or program is a good investment? Learn how veteran CSOs think about security investments, and develop your own rubric for evaluating where to best make your next security improvement.
-
How do you design defenses against DDoS? And how do you think about them from a policy perspective?
-
How do humans make risk decisions, and are they good, bad, or something else?
-
How do the grand challenges of the future look like the grand challenges of the past?
-
What does a Zero Trust journey look like? Explore how we migrated Akamai to a zero trust network access model, before that was even a phrase people knew.
Security Panels
-
Lenovo Late Night I.T: Cybersecurity: Trust No One
Join Baratunde Thurston, Tim Brown, and Andy Ellis as they demistify security.
-
Cyberweek 2021: Navigating the CISO-Vendor relationship
The panel discusses the do’s and don’ts of engagements between CSOs and early-stage startups, the concerns around long integration cycles, the value in quick implementations, and the need to show value quickly.
-
Cyberweek 2021: YL Ventures & Scale Fireside Chat
YL Ventures and Scale Venture Partners hosted a Cyber Week 2021 Fireside chat where Wendy Nather, Sounil Yu, Ryan Gurney, and Ariel Tseitlin discussed the cyber industry challenges and trends. They talked about the burning challenges and the basics that CSOs are still struggling with, and how ransomware attacks undermine our ability to recover. Other…
Security Blog
Security Podcasts
-
Cloud Security Reinvented: Jonathan Jaffe
https://orca.security/resources/podcast/?wchannelid=v7ih6xfqse&wmediaid=hil9bg18er Cloud computing is changing the world as we know it. So what impact does it have on the world of security?Jonathan Jaffe is the Chief Information Security Officer at Lemonade, a full-service consumer insurance company powered by artificial intelligence and behavioral economics and driven by social good. After years of experience in information security…
-
CISO Series: We’re very good at saying we care about diversity
https://cisoseries.com/were-very-good-at-saying-we-care-about-diversity/ It’s extremely easy to say you want to diversify. In fact, I’ll do it right now three times. We want diversity.We’re very pro diversity and it’s our focus for the next year.Diversity is a very important part of our security program.Please don’t ask to though look at the lack of diversity on our staff.…
-
Cloud Security Reinvented: Drew Daniels
https://orca.security/resources/podcast/?wchannelid=v7ih6xfqse&wmediaid=9cf8dpfxhk When it comes to information security and technology, Drew Daniels is the person to talk to. He believes information security can be a business driver as important as providing strong leadership.Having been in the industry before cloud computing, he’s also knowledgeable about the best pre and post-cloud practices. However, despite his long experience and…