-
How to CISO, Volume 1: The First 91 Days

Just want to download the eBook? Head over to How to CISO, Volume 1: The First 91 Days! It seems to be a rite of passage for all CISOs to, at some point in their career, write down their advice for other CISOs starting a new job, whether they are a first-time or veteran CISO.…
Security Talks
-
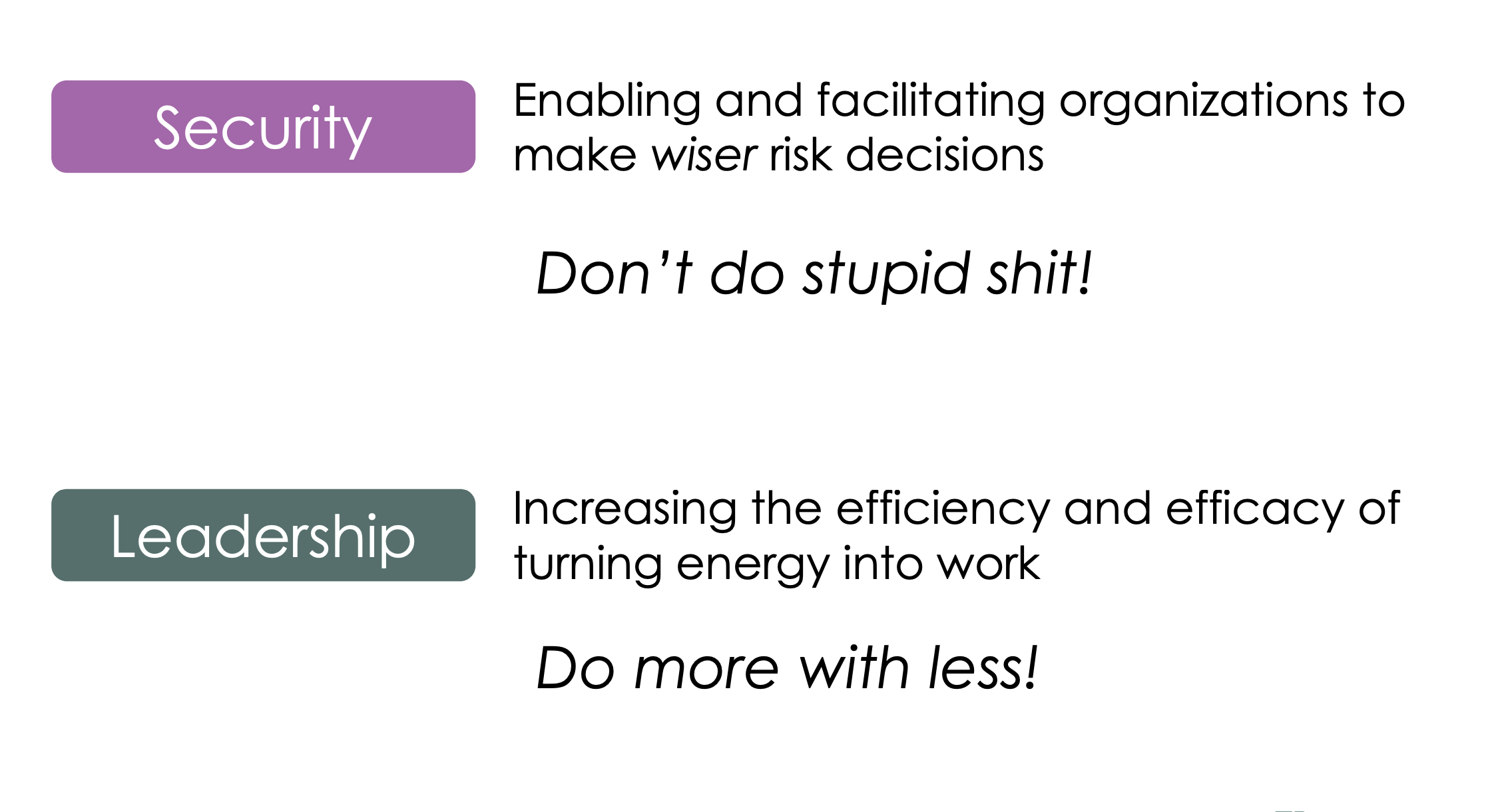
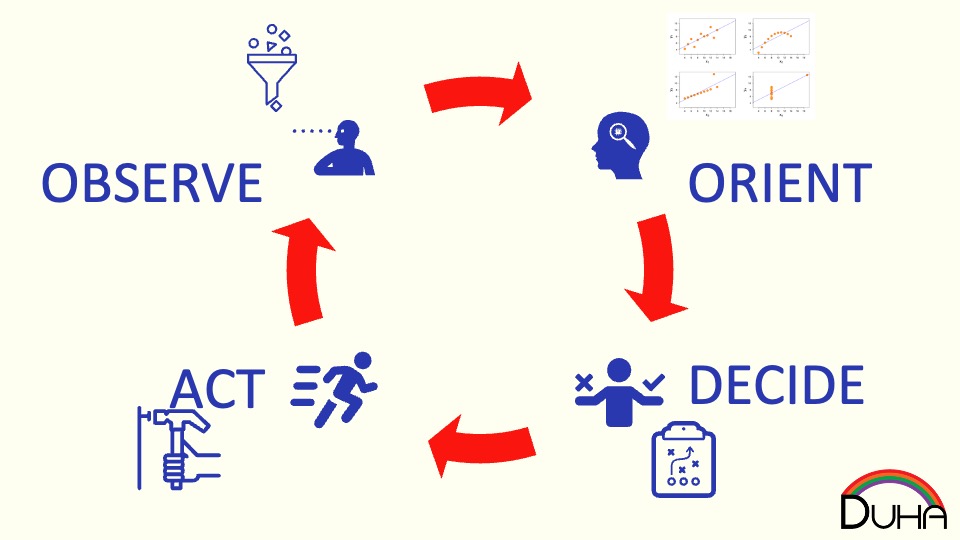
This talk delves into the intersection between security–helping make wiser risk choices–and leadership–getting more done with a lower energy cost. It draws on the lessons of the Six Leadership Disciplines and Humans are Awesome at Risk Management talks, providing a handful of examples of specific leadership skills to practice. The 24 skills in the matrix…
-
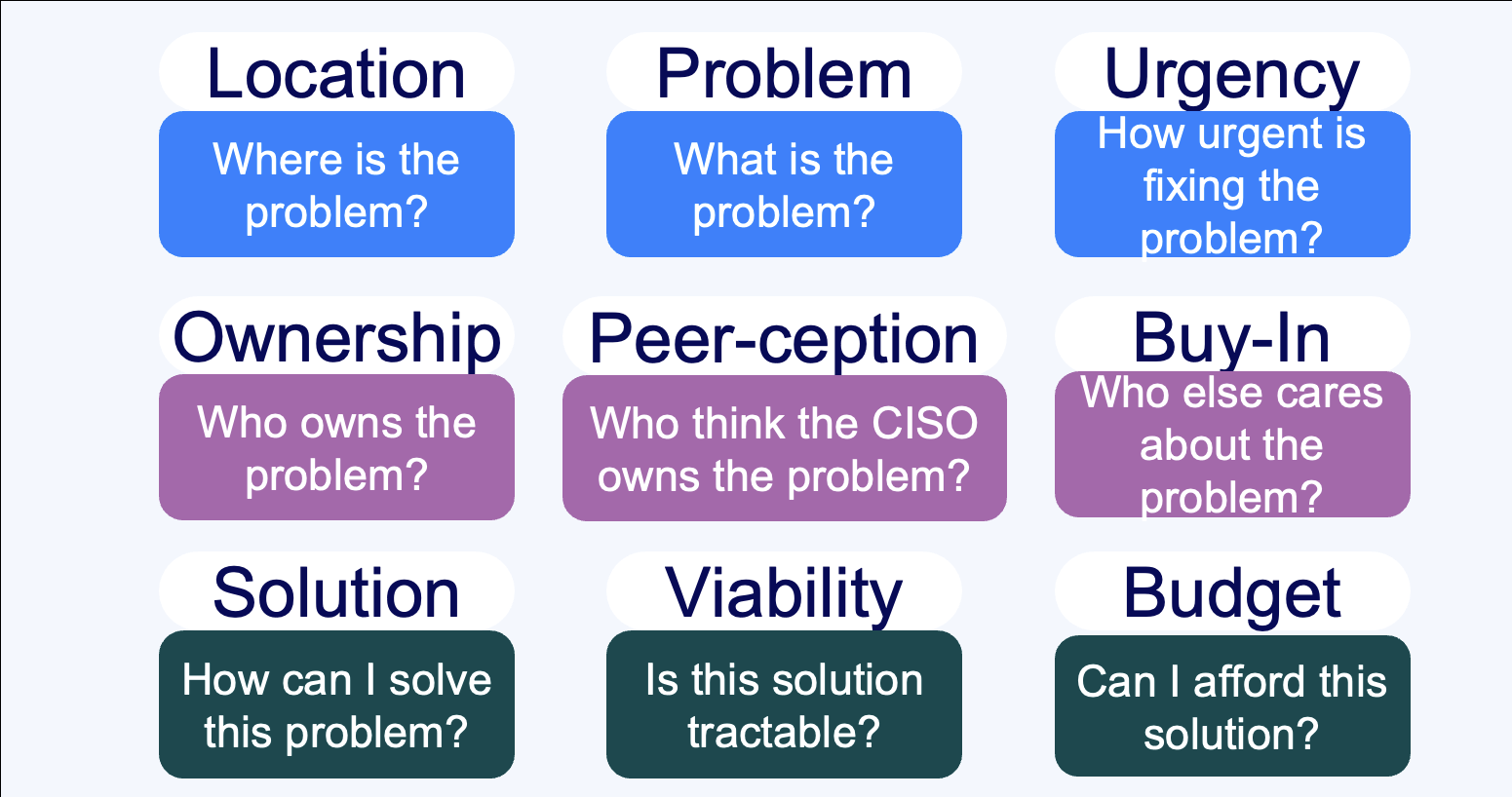
Summary Everybody sells, right? Wrong. Unless you’re taking an order and retiring your quota, you don’t sell – instead, you market. If you’re selling to a CISO, you need to understand the organizational dynamics that surround a CISO’s decision-making process. This talk walks through nine critical questions that CISOs need to understand the answers to…
-
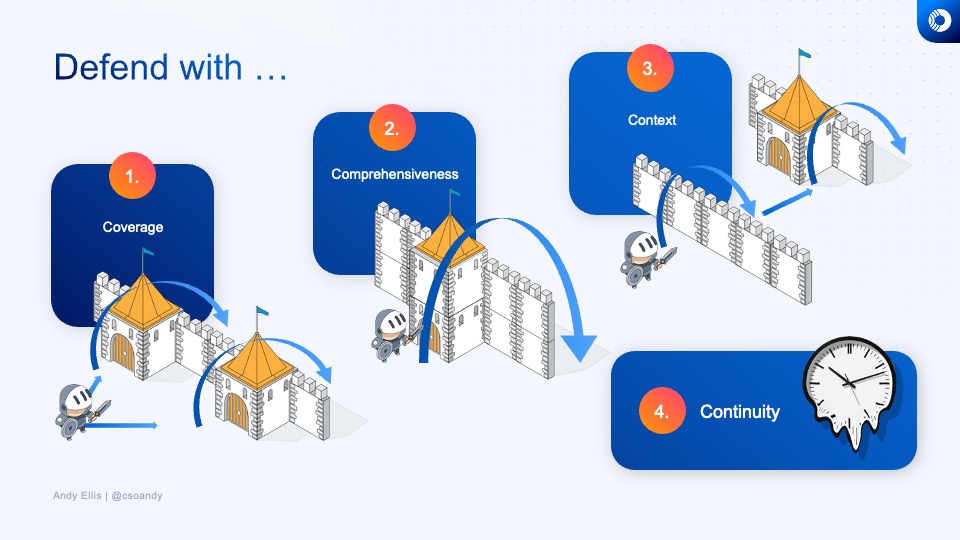
How do you know what to invest in next, or whether the time and energy that you’re spending on a security technology or program is a good investment? Learn how veteran CSOs think about security investments, and develop your own rubric for evaluating where to best make your next security improvement.
-
How do you design defenses against DDoS? And how do you think about them from a policy perspective?
-
How do humans make risk decisions, and are they good, bad, or something else?
-
How do the grand challenges of the future look like the grand challenges of the past?
-
What does a Zero Trust journey look like? Explore how we migrated Akamai to a zero trust network access model, before that was even a phrase people knew.
Security Panels
-
Lenovo Late Night I.T: Cybersecurity: Trust No One
Join Baratunde Thurston, Tim Brown, and Andy Ellis as they demistify security.
-
Cyberweek 2021: Navigating the CISO-Vendor relationship
The panel discusses the do’s and don’ts of engagements between CSOs and early-stage startups, the concerns around long integration cycles, the value in quick implementations, and the need to show value quickly.
-
Cyberweek 2021: YL Ventures & Scale Fireside Chat
YL Ventures and Scale Venture Partners hosted a Cyber Week 2021 Fireside chat where Wendy Nather, Sounil Yu, Ryan Gurney, and Ariel Tseitlin discussed the cyber industry challenges and trends. They talked about the burning challenges and the basics that CSOs are still struggling with, and how ransomware attacks undermine our ability to recover. Other…
Security Blog
-
Environmental Controls at Planetary Scale
Standard security frameworks often emphasize environmental controls, such as humidity sensors and fire suppression, to maximize mean time between critical failures (MTBCF) in data centers. However, the cost and effort of implementing these controls may not be worth it when operating in thousands of data centers globally. Instead, focusing on regional failover and addressing issues…
-
DNS reflection defense
DDoS attacks exceeding 100 Gbps, particularly DNS reflection attacks, have become prevalent. Understanding DNS operation is crucial for effective defense. Filtering, DNS server protection, redundancy, anycast, segregation, response handling, and rate limiting are key measures to mitigate attacks and ensure robust architecture.
-
How big is 300 Gbps, really?
The 300 Gbps attack on SpamHaus may appear significant, but considering attacker capacity, leverage, and target resilience, it becomes more manageable. Reflected DNS traffic can be easily dropped, making it less effective than other tactics. BroBot botnets pose comparable challenges with varied techniques.
-
Risk compensation
Collaborating with business partners to manage risk is a challenge for the security profession. Avoiding the role of sole custodians, we should engage partners in risk discussions and empower them to analyze risks themselves. By fostering belief and behavioral changes, we can achieve effective risk management.
-
Leveling up Security Awareness
Security awareness has become a contentious issue as organizations resort to generic, checkbox-based computer-based training (CBT) programs. To improve, it’s crucial to separate policy awareness from true security awareness. Instead of wasting resources on annual CBT, create an automated system for employees to check a box, and then focus on targeted, engaging, and incentivized security…
-
Understanding and increasing value
In assessing the value we provide to a business, we must understand its capabilities: the ratio of value over resources. While value is often difficult to measure, we can gauge capabilities by considering skill, effort, and effectiveness. Skill is the ease with which a task is accomplished, effort reflects our approach, and effectiveness depends on…
-
The value of professional certifications
As I prepare to join a panel discussion on information security certifications, the topic of their intrinsic value comes to mind. Examining different models, such as guild certificates, practitioner’s certificates, and reputational certificates, it becomes clear that infosec certifications lean more towards being reputational. However, reputational certificates are only as valuable as the reputation of…
-
Take Over, Bos’n!
Eleven years ago, Danny Lewin was tragically killed. But this story takes us back twelve years prior, when Danny’s relentless spirit inspired me to revolutionize the web. Despite initial doubts, Danny’s unwavering belief in our product led us to create a groundbreaking security model. It took time, but eventually, we transformed e-commerce, e-government, and business…
-
Security Subsistence Syndrome
Security subsistence syndrome (SSS) is a mindset in organizations that believe they have no security choices due to underfunding, leading them to minimally spend on perceived regulatory requirements. It’s an attitude of doing the bare minimum, resulting in lowered expectations and a lack of security value. Breaking free from SSS involves strategic steps that can…
-
Enterprise InfoSec Lessons from the TSA
The TSA’s security practices serve as a valuable analogy for enterprise information security. Like the TSA, security teams often focus on metrics that don’t align with the business’s goals. Weak authentication, limited logging, and reliance on outdated technologies are akin to enterprise practices that hinder effectiveness. Instead, a shift towards flexible security techniques that align…
Security Podcasts
-
We’re Here. We’re Highly Unqualified. Get Used To It.
https://cisoseries.com/were-here-were-highly-unqualified-get-used-to-it/ “Does anyone else feel like the security field is attracting a lot of low-quality people and hurting our reputation,” asked a redditor on the cybersecurity subreddit who remembers a time when security personnel were seen as highly experienced technologists. But now they believe people view cybersecurity as an easy tech job to break into…
-
Cloud Security Reinvented: Jadee Hanson
https://open.spotify.com/episode/1X6yRFgxfYymbG3qYO1hti 💡 Name: Jadee Hanson💡 What she does: She’s the CIO and CISO at Code42.💡 Noteworthy: As CIO and CISO at Code42, Jadee Hanson leads global risk and compliance, security operations, incident response, and insider threat monitoring and investigations. She brings more than 17 years of experience in information security and a proven track record of building security…
-
Sound Security Advice That’s Perfect to Ignore
https://cisoseries.com/sound-security-advice-thats-perfect-to-ignore/ It appears our security awareness training is falling short at the point of taking any type of real action. While most people are aware of the need for secure passwords, they don’t create secure passwords. They are taking the easier way out rather than the secure path which isn’t that far from the easy…